TL;DR:
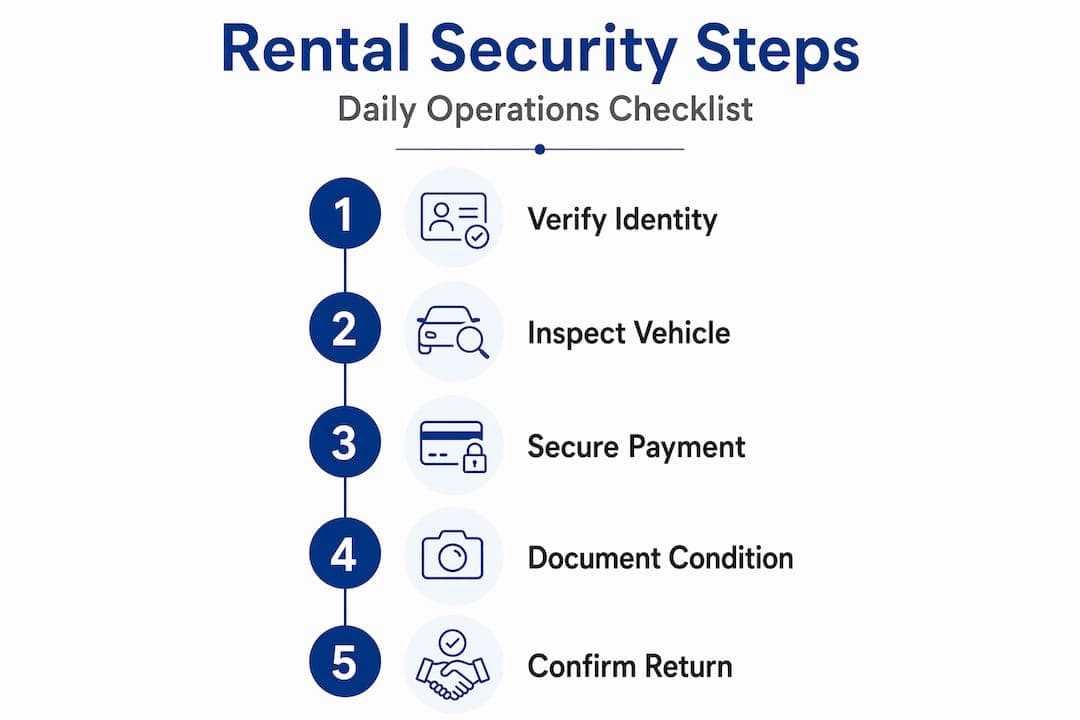
- Effective rental security requires understanding applicable risks, implementing documented processes, and maintaining ongoing compliance.
- A strong security architecture, including optimized payment workflows and trained staff, is essential for protecting assets and customer data.
Running a car rental business means you are simultaneously managing physical assets worth hundreds of thousands of dollars, processing sensitive payment data, and verifying the identities of strangers who drive your vehicles away. This rental security methods guide exists because the risks sitting at that intersection, vehicle theft, payment fraud, identity misuse, and data breaches, are growing more sophisticated every year. Small and medium rental operators often bear the same compliance obligations as large chains but with far leaner teams. The steps ahead will give you a practical, regulation-aligned framework to protect your fleet, your customers, and your business.
Table of Contents
- Understanding your rental security requirements and risks
- Preparing your rental business for robust security
- Executing effective operational security methods
- Verifying and maintaining ongoing rental security compliance
- Why many rental security strategies fall short and how to truly secure your rental business
- Secure your car rental business with Nomora's software solutions
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Comprehensive security approach | Effective rental security combines vehicle protection, customer verification, data compliance, and staff training. |
| Plan before action | Documenting obligations and assets ensures security measures align with legal requirements and business needs. |
| Payment processing design matters | Outsourcing card data handling reduces PCI compliance complexity and risk. |
| Operational consistency is key | Daily use of checklists and photo inspections protects assets and supports dispute resolution. |
| Sustain security over time | Ongoing audits, training refreshers, and documented vulnerability scans maintain effective protection. |
Understanding your rental security requirements and risks
Before you deploy any tools or write any policies, you need a clear picture of what you are actually protecting against. Rental security is not a single discipline. It spans vehicle protection, customer data handling, payment processing, and counter-terrorism awareness, each with its own regulatory expectations.
In the UK, the RVSS code of practice provides a government-backed benchmark. The UK RVSS code of practice mandates counter-terrorism, fraud prevention, and data protection as key rental vehicle security elements. That means your obligations extend well beyond fitting a GPS tracker. You are expected to have documented security plans, trained staff, identity verification procedures, and active engagement with law enforcement channels.
On the payment side, PCI DSS (Payment Card Industry Data Security Standard) is the governing framework for how you handle card transactions. The compliance burden you face depends heavily on your payment architecture. PCI DSS SAQ eligibility depends on how card payments are handled, which directly influences how much documentation and testing you must complete each year.
Key risk categories for rental businesses
- Vehicle theft and unauthorized use including misuse in criminal or terrorist acts
- Identity and document fraud at the point of rental or online booking
- Payment fraud through stolen card details or chargebacks
- Data breaches exposing customer personal information stored in your systems
- Operational disputes around vehicle condition and damage liability
| Risk category | Primary impact | Regulatory reference |
|---|---|---|
| Vehicle misuse | Asset loss, liability exposure | RVSS code of practice |
| Identity fraud | Financial loss, reputational damage | RVSS identity verification requirements |
| Payment fraud | Financial loss, chargeback costs | PCI DSS compliance |
| Data breach | Legal penalties, customer trust loss | GDPR, data protection law |
| Damage disputes | Revenue loss, legal costs | Internal inspection policies |
Pro Tip: Many operators treat these risk categories as separate problems. They are not. A single fraudulent rental can involve a stolen identity, a cloned card, and a stolen vehicle all at once. Your fraud prevention strategies need to address them as interconnected threats.
With the security environment clear, let's prepare your business to meet these requirements effectively.
Preparing your rental business for robust security
Good security does not start with buying software or installing cameras. It starts on paper. NIST advises small businesses to establish documented cybersecurity plans covering legal obligations and critical assets before deploying any tools. That principle applies directly to rental operations, where the variety of assets and data types means a generic checklist will not cut it.
Steps to build your security foundation
-
Document your legal and regulatory obligations. List every requirement that applies to your business, RVSS, PCI DSS, GDPR, and any local licensing conditions. Put names and deadlines against each one.
-
Identify your critical assets. Vehicles are the obvious entry, but your list should also include customer identity documents, payment card data, booking records, and staff access credentials.
-
Design your payment architecture deliberately. PCI SAQ eligibility is optimized by routing card transactions through a validated third-party payment processor, keeping raw card data off your own systems entirely. This can reduce you from a complex SAQ D questionnaire down to a much simpler SAQ A.
-
Write a security delivery plan. This document assigns responsibility for each security measure, sets a timeline for implementation, and creates a review schedule. It is also what you would show a regulator or insurer if questioned.
-
Audit your current staff knowledge. Before training, find out what your team actually knows about fraud indicators, data handling, and suspicious behavior reporting. The gaps will shape your training program.
Staff training priorities
Your team is both your most important security asset and your most common vulnerability. Training should cover:
- Counter-terrorism awareness: Recognizing unusual rental patterns, cash-only payment pressure, or requests for large commercial vehicles with vague purposes
- Fraud detection: Identifying mismatched ID documents, inconsistent customer behavior, or card payment anomalies
- Data protection: Understanding what customer data can and cannot be retained, how to store it, and what to do in a breach scenario
- Escalation procedures: Knowing exactly who to call, whether that is a manager, law enforcement, or a payment processor's fraud team
| Training topic | Delivery method | Recommended frequency |
|---|---|---|
| Counter-terrorism awareness | In-person or video module | Annually, plus on hire |
| Fraud detection | Scenario-based exercises | Every 6 months |
| Data protection | Policy review and quiz | Annually |
| Escalation procedures | Role-play drills | Quarterly |
Pro Tip: Use your rental fleet security checklist as the backbone of staff training. When staff practice the checklist in real handover scenarios, security behaviors become routine rather than reactive.
Once prepared, it's time to put practical security methods into action in daily operations.
Executing effective operational security methods
Day-to-day execution is where security plans either hold up or fall apart. This section covers the specific actions that protect your vehicles, your payment environment, and your customers at every transaction point.

Identity verification at vehicle handover
The RVSS code specifies identity verification, security technology installation, and staff vigilance as core methods for mitigating rental risks. Practically, this means:
- Check a valid, unexpired government-issued photo ID against the person standing in front of you. Do not rely solely on online pre-verification.
- Cross-reference the name on the ID with the payment card being used.
- For commercial vehicle rentals, apply enhanced checks including business verification and the purpose of use.
- Record the verification step in your rental management system with a timestamp.
Vehicle security technology
- Immobilizers are a legal requirement in many jurisdictions and a baseline deterrent
- GPS tracking devices allow real-time location monitoring and recovery support if a vehicle is stolen or overdue
- Telematics can flag abnormal usage patterns, high-speed driving outside permitted zones, or ignition activity at odd hours
Payment security in practice
Accept electronic payments only, processed through a PCI-validated third party. Never enter card numbers manually into a system that stores them. If a customer insists on cash for a large rental, treat that as a risk indicator and apply additional identity verification.
Vehicle condition documentation
Photo documentation at vehicle handover and return reduces disputes and strengthens your position in incident response. Your process should be:
- Photograph all four sides of the vehicle plus the interior before rental
- Timestamp and attach photos to the digital rental agreement
- Repeat the same process at return
- Store records against the customer booking for a minimum period aligned with your legal obligations
| Security method | Protects against | Required by |
|---|---|---|
| Identity verification | Fraud, misuse | RVSS code |
| GPS tracking | Theft, overdue returns | Best practice |
| Payment via validated third party | Card fraud, PCI breach | PCI DSS |
| Timestamped photo documentation | Damage disputes | Internal policy |
| Staff vigilance reporting | Terrorism, criminal misuse | RVSS code |
Pro Tip: Review your vehicle inspection practices and your digital rental agreements as a paired process. A thorough inspection only protects you if it is captured in a signed, timestamped document the customer has acknowledged.
After implementing these procedures, regular verification and compliance checks maintain security over time.