TL;DR:
- Remote access allows car rental businesses to manage fleets and serve customers from any location.
- Cloud-based solutions improve efficiency, scalability, and security while reducing administrative overhead.
- Successful implementation relies on staff training, staged rollout, and continuous monitoring of key metrics.
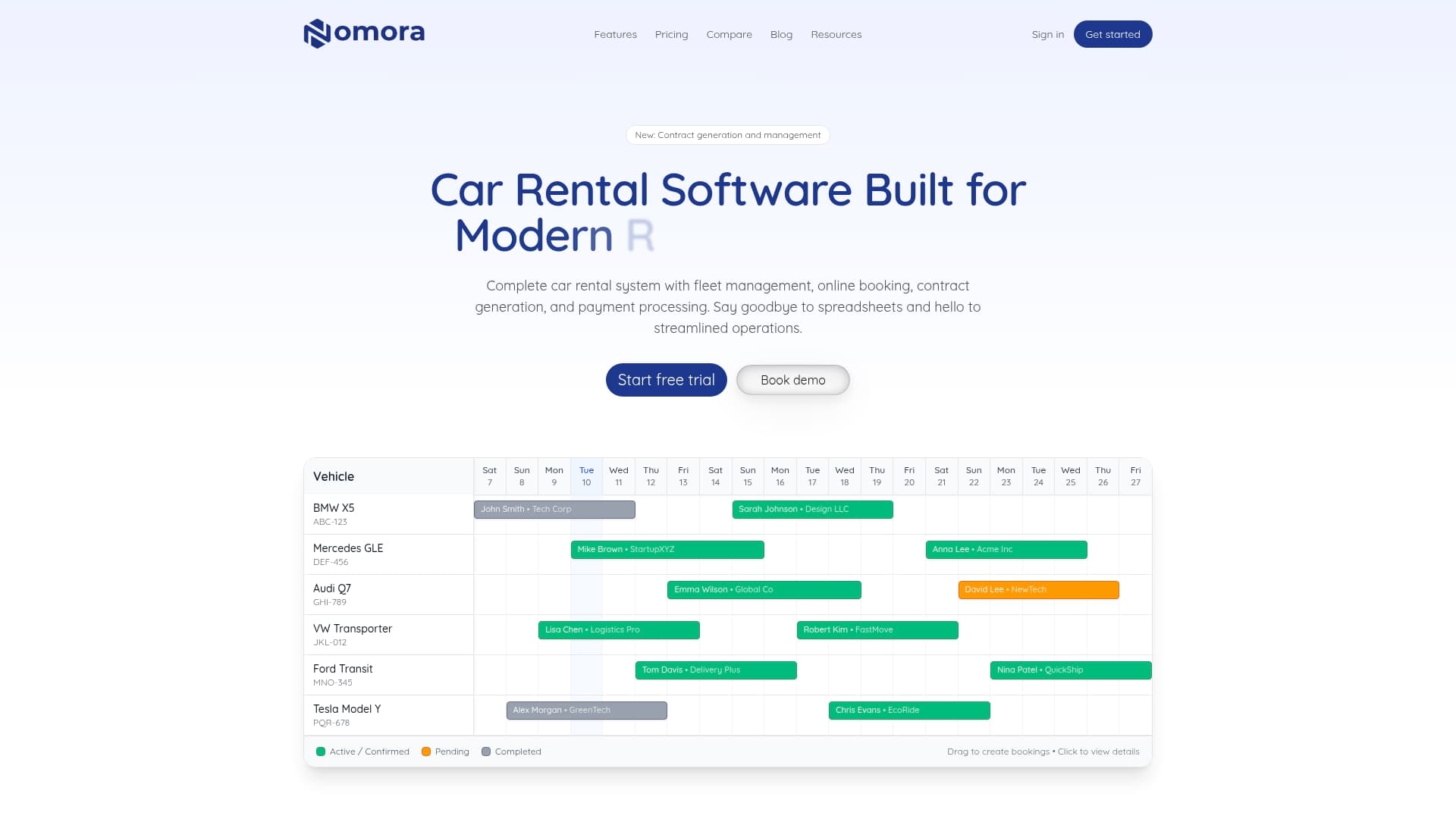
Running a car rental business used to mean being physically present to manage every booking, hand off every key, and reconcile every payment at the end of the day. That model is quickly becoming obsolete. Cloud-based remote access is no longer a luxury reserved for large franchise networks with deep IT budgets. Small and mid-sized rental operators are now using these same technologies to manage fleets from anywhere, serve customers faster, and reduce the administrative overhead that drains time and profit. This article walks you through exactly what remote access means for your operation, which cloud technologies matter most, and how to implement them securely and efficiently.
Table of Contents
- Defining remote access in car rental operations
- Cloud technologies transforming remote rental operations
- Steps to enable secure remote access in your rental business
- Unlocking efficiency: practical outcomes of remote access
- What most guides overlook: the real secret to successful remote access
- Next steps: streamline your rental operation with Nomora
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Remote access advantages | Small rental businesses can now utilize remote access for greater flexibility, efficiency, and customer satisfaction. |
| Cloud technology impact | Migrating to cloud solutions streamlines operations and provides scalable, secure management with fast ROI. |
| Implementation steps | Successful adoption requires PCI-compliance, encrypted systems, ongoing updates, and staff training. |
| Continuous improvement | Monitor metrics monthly to optimize fleet utilization and realize ongoing operational benefits. |
Defining remote access in car rental operations
Remote access, in the context of a car rental business, means that authorized people, whether managers, staff, or customers, can interact with your rental systems and vehicles from any location with an internet connection. Think of your rental management software as the central nervous system of your operation. Remote access keeps that system responsive even when you are not physically in the office.
This is not a vague concept. In practice, remote access enables a wide range of critical functions:
- Online booking management: Staff can create, modify, or cancel reservations from any device without being tied to a front desk terminal.
- Fleet status monitoring: Managers can check vehicle availability, mileage, location, and maintenance status in real time.
- Digital contract generation: Rental agreements can be drafted, signed, and stored electronically without paper.
- Remote vehicle unlocking: Customers can unlock and access vehicles through a mobile app, eliminating the need for in-person key exchanges.
- Payment processing: Transactions are handled digitally, reducing cash handling and enabling instant receipts.
- Data analytics access: Business owners can pull utilization reports, revenue data, and customer records from any location.
One of the most persistent misconceptions is that remote access is only practical for large rental chains with dedicated IT teams. In reality, modern cloud solutions for car rentals are designed with small operators in mind, offering plug-and-play setup, intuitive interfaces, and pricing that scales with your fleet size.
Another common misunderstanding is that remote access creates security vulnerabilities. The opposite is true when implemented correctly. Keeping your systems and your customers' payment data secure is non-negotiable, and responsible vendors build that protection in from the start. As highlighted in security vulnerability research, the best way to mitigate risk is through PCI-compliant payments, data encryption, regular security patching, and network segmentation while avoiding cheap, unpatched software that leaves your operation exposed.
"Remote access is not about removing human oversight. It is about giving the right people the right information and control at the right time, from wherever they happen to be."
Understanding the full scope of rental software features helps operators appreciate which capabilities matter most for their specific business model. A two-location operation has different remote access priorities than a solo operator managing a five-car fleet, but both benefit from the core principles: real-time visibility, secure data handling, and flexible access controls.
With remote access defined, let's explore how cloud solutions play a crucial role.
Cloud technologies transforming remote rental operations
Cloud platforms have fundamentally changed what is possible for small and mid-sized rental businesses. Where traditional on-premise software required local servers, manual backups, and IT maintenance contracts, cloud-based systems deliver the same power through a browser or mobile app, with updates happening automatically in the background.
The core cloud technologies most relevant to car rental operations fall into a few categories:
- SaaS rental management platforms: All-in-one systems that handle reservations, contracts, payments, fleet tracking, and reporting through a single cloud-hosted interface.
- GPS telematics integration: Real-time vehicle tracking feeds data directly into your rental platform, giving you location, speed, fuel levels, and trip history at a glance.
- Payment gateway APIs: Secure, cloud-hosted payment processors connect to your rental system, enabling card-on-file charges, deposits, and automated invoicing.
- Cloud storage and document management: Contracts, IDs, and incident reports are stored securely in the cloud and accessible to authorized staff from any device.
The hybrid telematics-cloud approach is particularly powerful. According to small business cloud guidance, combining telematics hardware in your vehicles with a cloud management platform yields the fastest ROI through improvements in fleet utilization and fuel savings. Real-time data helps you identify underused vehicles, optimize scheduling, and catch maintenance issues before they become expensive breakdowns.
Here is a direct comparison of on-premise versus cloud-based systems to help you assess where your business currently stands:
| Feature | On-premise systems | Cloud-based systems |
|---|---|---|
| Upfront cost | High (hardware and licenses) | Low (monthly subscription) |
| Scalability | Limited and expensive | Flexible and immediate |
| Security updates | Manual, often delayed | Automatic and continuous |
| Remote access | Restricted or unavailable | Full access from any device |
| Data backup | Manual or local | Automated and offsite |
| Integration options | Limited and costly | Extensive via APIs |
Using a system integration guide can help you map out which existing tools such as accounting software, GPS providers, and payment processors can connect to a new cloud platform without requiring you to start from scratch. Most modern platforms also offer rental integrations that slot directly into tools you may already be using, which dramatically reduces migration complexity.
Maximizing fleet utilization strategies through cloud data is one of the clearest paths to improved profitability. When you can see in real time which vehicles are sitting idle and which are generating revenue, you make smarter decisions about pricing, repositioning, and fleet expansion.

Pro Tip: When migrating to cloud software, start with a non-critical workflow such as internal reporting or customer communications before moving reservations and payments. This reduces disruption and gives your team time to build confidence with the new system before it handles mission-critical transactions.
Having seen the value of cloud technologies, the next step is choosing and implementing them effectively.
Steps to enable secure remote access in your rental business
Implementing remote access is not simply about purchasing software and flipping a switch. A structured approach protects your business, your customers, and your reputation. Here are the key steps to follow:
-
Assess your current setup and priorities. Identify your fleet size, the number of locations you manage, your current booking volume, and the biggest pain points in your daily workflow. Are customers waiting too long for check-in? Are you losing track of vehicle locations? Understanding these gaps shapes which remote access features to prioritize first.
-
Select a PCI-compliant, encrypted management platform. Not all rental software is built with security as a priority. Insist on platforms that offer PCI-DSS-compliant payment processing, end-to-end data encryption, and clear documentation of their security practices. This protects your customers' payment information and shields your business from liability.
-
Implement network segmentation. If your operation uses a local network in an office or lot, segment that network so that customer-facing devices, internal management systems, and payment terminals operate on separate network zones. This limits the spread of any potential breach.
-
Establish a regular patching schedule. Outdated software is one of the most common entry points for security incidents. Work with your software provider to ensure that updates and security patches are applied promptly. As vulnerability research confirms, avoiding cheap unpatched software is essential because the cost of a data breach far outweighs the savings from a lower-priced tool.
-
Set up role-based access controls. Not every employee needs access to every part of your system. Configure user permissions so that front-line staff can manage bookings and check-ins while only managers and owners can access financial reports and system settings.
-
Test your setup with a pilot group. Before rolling out remote access to your full team or customer base, run a controlled pilot with a small group of staff or a single vehicle category. Gather feedback, identify friction points, and resolve them before scaling.
Here is a quick reference table for common vulnerabilities and how to address them:
| Vulnerability | Risk level | Mitigation strategy |
|---|---|---|
| Unpatched software | High | Automated updates and regular audits |
| Weak passwords | High | Multi-factor authentication (MFA) |
| Unsegmented networks | Medium | Network segmentation by function |
| Non-compliant payments | Critical | PCI-DSS-compliant payment gateway |
| Unencrypted data storage | High | End-to-end encryption at rest and in transit |
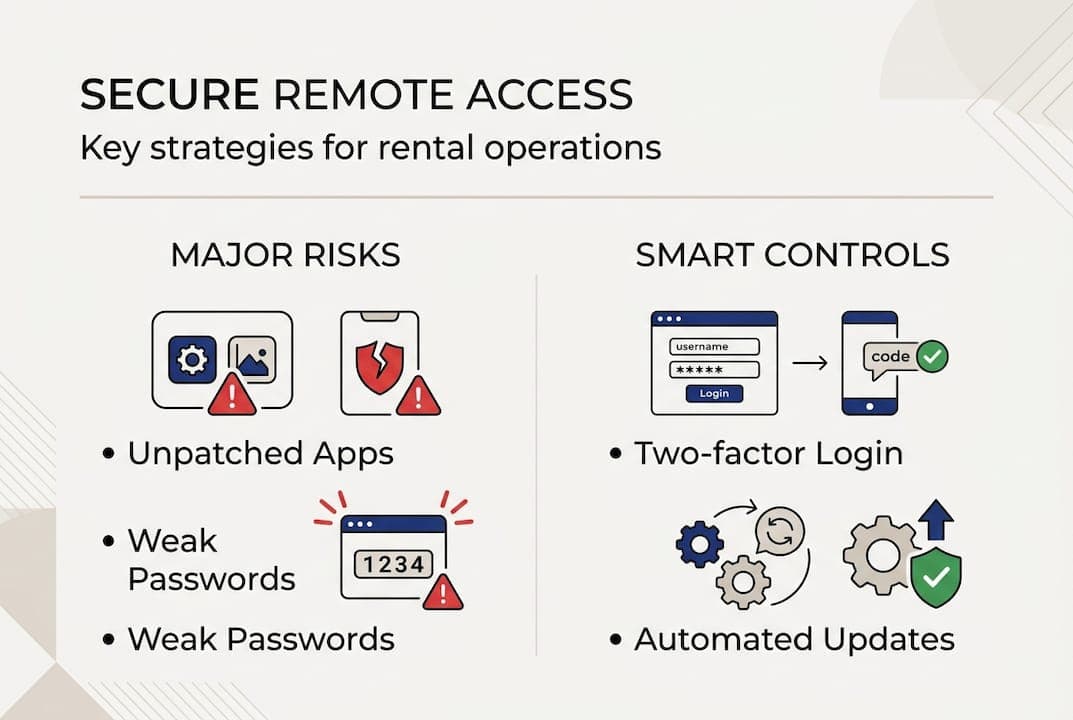
Reviewing fraud prevention strategies specific to the rental industry is also a smart move during this phase. Rental businesses face unique fraud risks, from identity theft to unauthorized vehicle use, and your remote access setup should account for these scenarios from the start. Pairing that knowledge with real-time tracking tips adds another layer of protection and visibility across your entire fleet.
Pro Tip: Never let cost savings lead you toward unpatched or unsupported software. A single security incident can result in regulatory fines, customer loss, and reputational damage that far exceeds what you saved on the software subscription.
After a secure implementation, continuous improvement is essential for maximum benefit.